Digital Risk Protection 101: What Is Digital Risk Protection? Complete Guide for Middle East & African Enterprises
Digital risk protection is no longer optional for Middle East and Africa enterprises. Learn the 9 modules of DRP solutions, why regulators require it, implementation timelines, and how to safeguard your organization from external digital threats.
Digital risk protection and digital risks are regulatory requirements across the Middle East and Africa. We've implemented Digital Risk Protection solutions at 150+ organizations to mitigate digital risks and safeguard digital assets. A data leak can destroy your brand reputation. Leaked credentials expose your digital environment. Here's what we've learned: most security teams don't understand what digital risk protection service key capabilities do, or why it matters beyond compliance.
Curious about your digital risk posture?
We assess digital risk in one day. Most organizations discover threats they didn't know existed. No obligation. Just clarity.
Key Takeaways
What Is Digital Risk Protection? Understanding Digital Risks and DRP Platforms
Digital risks exist everywhere. Your brand gets counterfeited on marketplaces you don't own. Executives get impersonated through phishing campaigns. Your digital assets and credentials appear on the dark web. Vendors get breached. Cloud infrastructure sits exposed. Malware spreads. These threats exist outside your network perimeter where traditional cybersecurity tools can't see them.
Digital risk protection safeguard your organization from these external threats. A drp solution helps mitigate digital risks and protect digital assets through continuous monitoring, intelligence gathering, and rapid response. Digital risk protection service provides key capabilities including brand monitoring, darkweb scanning, executive protection, asset discovery, vendor assessment, threat intelligence, and takedowns.
The Digital Risks Digital Risk Protection Service Helps Mitigate:
Brand Threats: Counterfeit products, fake websites, brand impersonation accounts, brand abuse on social media, phishing campaigns targeting customers. These damage brand reputation and customer trust and cost revenue.
Executive Threats: Fake profiles impersonating leaders, personal impersonation, phishing attacks targeting executives. These are personal threats affecting individuals.
Data Threats: Leaked credentials sold on paste sites and dark web, customer data breached, ransomware claims on dark web forums, intellectual property stolen. These threaten sensitive data and digital assets. A data leak can damage brand reputation for years.
Infrastructure Threats: Public cloud buckets, exposed databases, API keys committed, vulnerable systems, malware-infected assets. These threaten organization's digital assets and digital footprint.
Supply Chain Threats: Vendor breaches become your cyber risk. Unvetted security practices. Un-contracted security requirements. Supply chain risk threatens your organization's digital assets through third parties.
"Most organizations are blind to external threats. You can have perfect firewalls and still get breached through a counterfeit website or leaked credentials on the dark web. That's where the blind spot is."— Security Director, Regional Financial Institution
Safeguard Your Digital Assets
Digital risk protection is no longer optional. Get a free assessment of your digital risk posture and discover threats you didn't know existed.
What Digital Risk Protection Service Key Capabilities Actually Provide
Digital risk protection service provides continuous threat monitoring and actionable intelligence about threats that originate outside your organization. This includes monitoring your brand, executives, data, infrastructure, and supply chain on the dark web, social media, web forums, and the internet at large.
A drp solution provides key capabilities including identifying and mitigating threats, detection and response, threat monitoring, and intelligence feeds. DRP platforms work together to safeguard digital assets and mitigate digital risks proactively. DRP software helps prevent data leaks and automate risk mitigation.
DRP vendors offer tools that scan the internet continuously. DRP tools provide actionable intelligence about threats in your digital environment. DRP alerts notify your team when threats are detected. Digital risk protection software automates much of the threat monitoring and response process.
How Digital Risk Protection Differs from Traditional Cybersecurity Tools:
Traditional cybersecurity tools protect what's inside your network. Digital risk protection service safeguards what's outside—your external digital assets, brand presence, and supply chain on the internet perimeter. DRP extends protection beyond your firewall perimeter.
Traditional cybersecurity responds to attacks. Digital risk protection identifies threats before they attack. DRP vs traditional approaches represent fundamentally different security postures and risk mitigation strategies.
"Traditional security is essential, but it's only half the equation. It's like having locks on your doors but not knowing what threats exist in your neighborhood. Digital risk protection is knowing what's out there."-Cybersecurity Architect, Multi-National Organization
How Digital Risk Protection Service Works:
Monitoring systems scan the internet 24/7 for organization keywords on dark web forums, paste sites, social media, web forums, and elsewhere. Analysis determines if matches are legitimate or threats. Identification of threats by severity. Response and takedowns. Continuous threat monitoring and follow-up. DRP tools scan automatically and provide actionable alerts.
Ready to understand your digital risk posture?
Our assessment identifies threats to your digital assets and creates an action plan specific to your organization's risk profile.
Why Organizations Need Digital Risk Protection Now: Digital Risks Are Growing
Regulators Require Digital Risk Protection Service and Key Capabilities
UAE's Central Bank requires digital risk protection to mitigate cyber risk. Saudi Arabia's SAMA mandates threat intelligence. Every regulator across the region requires drp solutions to help mitigate digital risks and protect digital assets.
Security teams need to demonstrate they can mitigate threats through documented risk assessments, evidence of monitoring, and response plans. Most organizations implement digital risk protection because regulators require it. The real value comes from threat discovery, breach prevention, and brand recovery.
Digital Risks Cost Real Money
Counterfeits damage customer trust and revenue. One regional ecommerce company discovered 10,000+ counterfeit sellers costing significant revenue. When discovered, brand damage was worse than direct loss.
Vendor breaches affect your organization's cyber risk and digital assets. Cloud misconfigurations expose sensitive data. Executives impersonated in phishing campaigns. These situations overwhelm security teams and damage reputation.
"A single counterfeit incident doesn't just cost revenue. It damages brand reputation for years. We've seen organizations lose 10-20% of customer trust in months because customers started questioning whether their products were real."— Brand Protection Specialist, Ecommerce Sector
The Threat Landscape Grows Daily
Criminal networks run counterfeit operations and phishing campaigns. Threat actors target specific sectors. Ransomware gangs claim breaches on dark web forums. Malware threats increase. Digital threats originating from external sources multiply.
150+ organizations we've worked with who implemented digital risk protection caught threats early. Those who waited dealt with crises. One regional fintech discovered executive credentials on dark web before breach. They prevented compromise through threat monitoring. That's what effective drp provides.
"Regulators require it now. But here's what we found: the real value isn't compliance. It's discovering threats you didn't know existed. One organization found 15,000 counterfeit seller accounts. They had no idea."— SOC Lead, UAE Operations
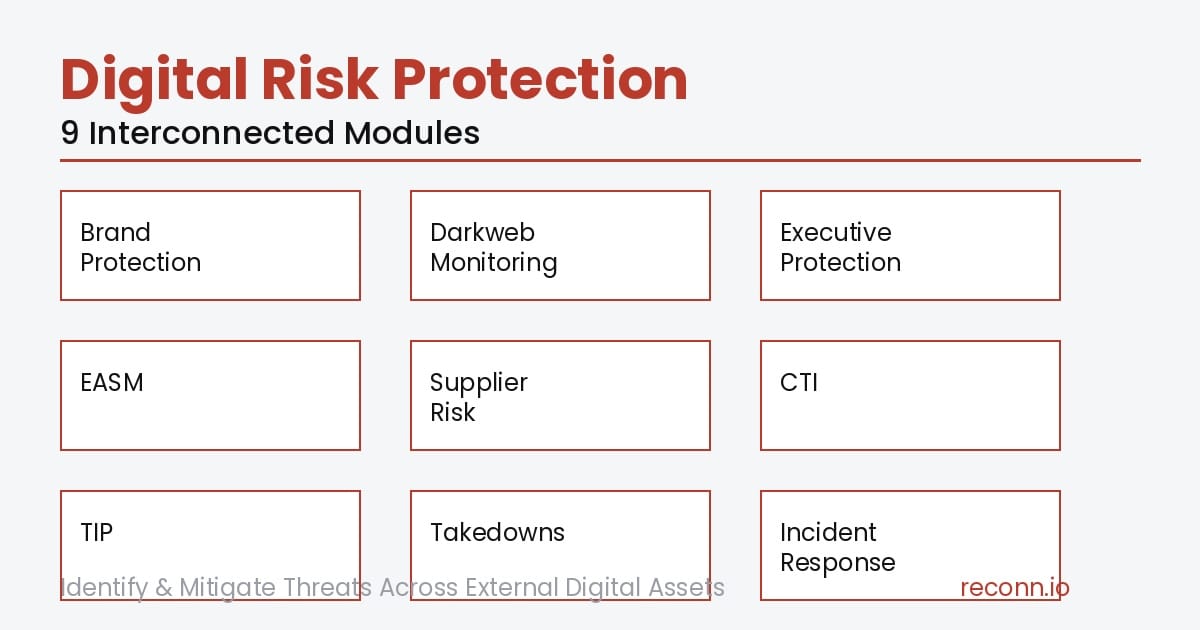
The 9 Modules of Digital Risk Protection: Key Capabilities
Digital risk protection isn't one tool. It's 9 interconnected capabilities. A digital risk protection solution covers identifying and mitigating threats across multiple vectors.
"We discovered our executive credentials on the dark web three months after a vendor breach. If we hadn't been monitoring, we wouldn't have known. Attackers would have had months to use those credentials. Instead, we rotated them in 24 hours." — Chief Information Security Officer, GCC Enterprise
Digital Risk Protection vs Traditional Cybersecurity Tools: DRP Strategies
Traditional cybersecurity tools protect internal networks. Digital risk protection service safeguards external digital assets and threats that originate outside your perimeter.
DRP vs traditional approaches differ fundamentally:
- Traditional: Reactive. DRP: Proactive identifying and mitigating.
- Traditional: Internal. DRP: External.
- Traditional: Current attacks. DRP: Future threats.
Effective drp provides what traditional cybersecurity tools cannot: external threat visibility, brand protection, darkweb intelligence, supply chain security.
Understanding the Internet: Surface Web, Deep Web, and Dark Web
Many people confuse the dark web with the deep web. Let's clarify what digital risk protection actually monitors.
How to Get Started: The Reconn Digital Risk Protection Initiative
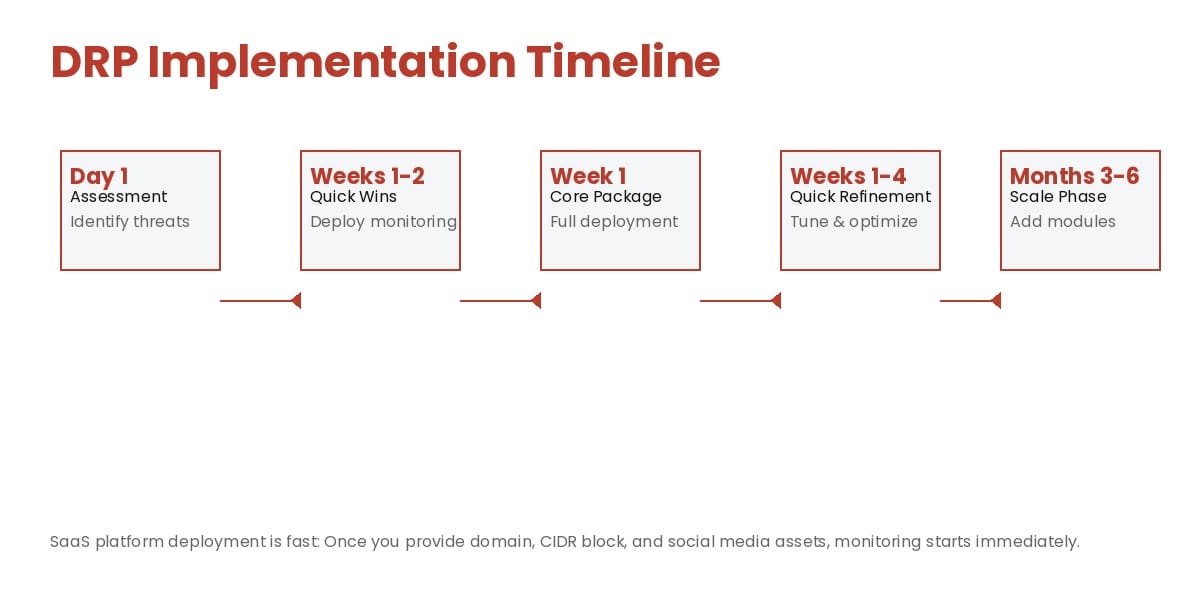
- Assess your digital risk footprint and digital environment
- Scan for counterfeits
- Check dark web and deep web for leaked credentials
- Analyze external assets
- Identify executive impersonation
- Evaluate vendor risks and supply chain risk
- Implement immediate protection through domain monitoring
- Marketplace scanning
- Social media scanning
- Takedowns
- Security teams see quick results
- DRP tools scan automatically and generate alerts
- Provide domain, CIDR block, and social media assets
- SaaS platform immediately starts scanning
- Brand Protection scanning across marketplaces and social media
- Darkweb and deep web monitoring for leaked credentials
- Executive Digital Protection detecting impersonation
- Takedown processes established
- CTI Feeds activated and providing actionable intelligence
- Initial scans produce results
- Threats identified and prioritized
- False positives tuned
- Alert thresholds refined
- Security teams receive actionable intelligence and alerts
- First takedowns occur
- Expand to EASM based on needs
- Implement Supplier Scoring
- Deploy Threat Intelligence Platform
- Expand modules based on discovered priorities
- DRP extends your risk mitigation across all 9 modules
"The speed surprised us. We expected 3-4 months. The platform was scanning our environment in week one. Quick wins appeared in two weeks. By month three, we had visibility we didn't think possible."— CTO, Saudi SaaS Startup
Let's assess your digital risk footprint in one day.
We scan your digital environment, identify threats, and show you exactly what you need. Most organizations see quick wins within 1-2 weeks.
FAQ: Digital Risk Protection for Middle East and Africa Enterprises
Digital Risk Protection Is No Longer Optional
Digital risks exist everywhere. Regulators demand drp solutions. Organizations implementing early are ahead. Those waiting catch up reactively.
Your digital risks grow as your footprint expands. Digital risk protection service key capabilities help you identify and mitigate threats before they become breaches.
Ready to Understand Your Digital Risk Posture?
One strategic drp solution covers all 9 modules. We've helped 150+ organizations implement digital risk protection.
Your digital risks won't disappear. Digital risk protection helps you find and fix them.
We've implemented digital risk protection for 150+ organizations across the Middle East and Africa. Let's talk about what your organization needs.



